Account & Call Log Validation – courtneymacneil1, 8096830290, 728362970, 7806661470, 7207120300, 7028778116, panarasss8, Tuzofalotaniz, Hexcisfesasjiz, 886279325026
Account and Call Log Validation – courtneymacneil1, 8096830290, 728362970, 7806661470, 7207120300, 7028778116, panarasss8, Tuzofalotaniz, Hexcisfesasjiz, 886279325026 invites a data-driven discussion on how probabilistic evidence, baseline checks, and audit trails can improve accuracy and resilience. The approach quantifies uncertainty, normalizes variations, and flags anomalies for review. It remains to assess how thresholds influence trust and whether automation can sustain integrity without eroding auditability. The next step questions what standards and controls should define robust validation.
What Account and Call Log Validation Is and Why It Matters
Account and Call Log Validation is the process of verifying that account details and call records are accurate, complete, and tamper-resistant.
This assessment treats data as probabilistic evidence, quantifying uncertainty and error rates.
It emphasizes auditability and resilience, enabling independent verification.
Key concepts include account validation and Call logs, guiding risk assessment, anomaly detection, and trust in telecommunication analytics.
How to Set Up Baseline Validations for Accounts and Numbers
Baseline validations for accounts and numbers build on the prior discussion of data integrity and tamper resistance by establishing objective, repeatable criteria that quantify uncertainty in account details and call logs.
The approach emphasizes probabilistic thresholds, independent verifications, and continuous sampling to assess trend stability.
Key measures include account validation procedures and log integrity checks, enabling transparent risk assessment and resilient data governance.
Detecting Anomalies and Handling Exceptions in Logs
Detecting anomalies and handling exceptions in logs requires a systematic, data-driven approach that distinguishes rare events from normal variation. The analysis emphasizes probabilistic thresholds, cross-checks, and contextual scoring to identify invalid accounts and irregular call log anomalies. Findings inform containment, verification, and targeted audits, while preserving overall system integrity and enabling responsive, freedom-respecting governance of data integrity.
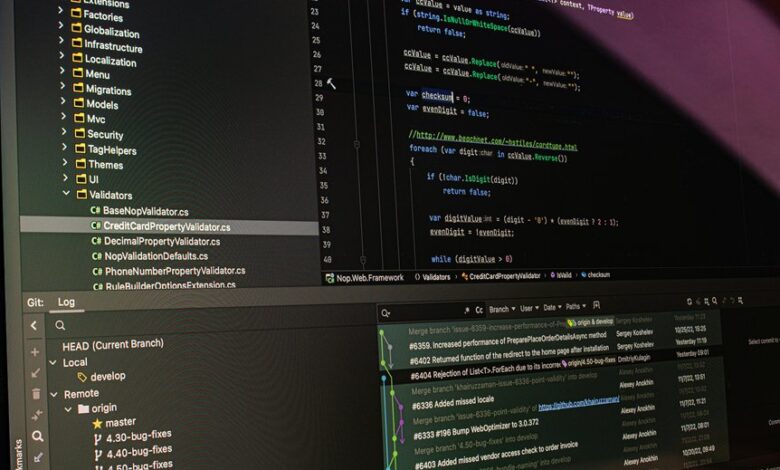
Automating Verification and Maintaining an Audit Trail
This framework emphasizes account validation and log integrity, enabling rapid anomaly detection, traceable decisions, and freedom-centered governance through transparent, defensible validation workflows.
Conclusion
The analysis concludes that account and call log validation behaves like a meticulous oracle, translating noisy signals into probabilistic certainties. Baselines act as sturdy anchors while anomaly scores reveal delicate shifts in trust. Logs, when kept with transparent audit trails, become reproducible evidence rather than murky folklore. In this data-driven framework, verification evolves from guesswork to quantified confidence, enabling resilient governance and auditable integrity, even as uncertainty ebbs and flows through each transactional tide.





