Identifier Integrity Check Batch – 18002675199, yf7.4yoril07-Mib, Lirafqarov, Adultsewech, goodpo4n, ыфмуакщьютуе, ea4266f2, What Is Buntrigyoz, Lewdozne, Cholilithiyasis
The Identifier Integrity Check Batch 18002675199 presents a structured provenance snapshot, linking IDs, contexts, and transformations to trace custody and timestamps. It invites methodical scrutiny of decoding tags, signatures, and potential anomalies. By detailing cryptographic proofs and audit trails, the batch frames authenticity as verifiable, reducing misinterpretation across datasets. The discussion invites careful evaluation of applicability and implementation, while signaling that further steps and clarifications are necessary to ensure rigorous integrity across contexts.
What the Identifier Integrity Check Batch Tells Us About Provenance
The Identifier Integrity Check Batch provides a structured record of provenance by capturing unique identifiers, their generation context, and any transformations applied during processing. It surveys linkage between sources, timestamps, and custody steps, while maintaining immutability through verifiable trails. This disciplined log reveals why peculiar insertions occur, noting unrelated topic metadata and off topic anomalies without compromising core lineage or trust.
Decoding the Tags: From Aliases to Signatures and What They Mean
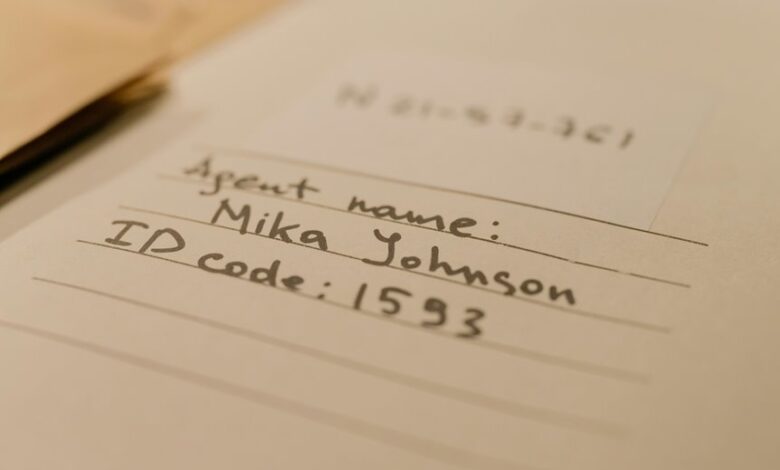
Decoding the tags requires a precise catalogue of their forms, meanings, and the transitions they undergo from alias to signature. The analysis presents decoding aliases as structured identifiers, clarifying signature meanings and their provenance insights. It supports authenticity detection and everyday verification, offering a disciplined framework. Detached observers compare variants, ensuring consistent interpretation and unambiguous provenance across contexts and datasets.
How Integrity Checks Detect Authenticity and Why It Matters
Integrity checks verify authenticity by comparing observed data against defined integrity constraints, cryptographic proofs, and provenance records. The method isolates deviations, exposing tampering, duplication, or replication inconsistencies. This validation reinforces trust, accountability, and traceability, supporting independent verification and auditability. An informed audience values freedom through transparent processes, while awareness of unrelated topic and off topic influences guards against misinterpretation and distraction.
Practical Pathways for Researchers and Developers: Implementing Verification Everyday
Practical pathways for researchers and developers to implement verification daily are outlined through a disciplined, repeatable approach: establish clear goals, select appropriate integrity mechanisms, and integrate verification checks into existing workflows. The approach emphasizes practical verification, batch provenance, and traceable audits. Systematic tooling, standardized data schemas, and continuous monitoring enable reproducible outcomes, minimize drift, and sustain rigorous authenticity across iterative development cycles without constraining creative exploration.
Frequently Asked Questions
How Often Should Integrity Checks Be Re-Run After Updates?
Updates should be re-run after each deployment and at least nightly for critical systems, with additional checks following major changes. This ensures frequency updates align with batch provenance, reducing drift and preserving integrity across environments.
Can False Positives Occur in Batch Provenance Checks?
False positives can occur in batch provenance checks, and parallel verification strategies mitigate risk; batch provenance anomalies may resemble genuine signals, demanding rigorous cross-validation, redundant logging, and threshold-tuning to preserve accuracy while preserving operational freedom.
Do Aliases Affect Cross-Platform Signature Verification?
Aliases can affect cross platform verification; aliases impact signature mapping across environments, requiring consistent canonicalization. In practice, verifiers pursue deterministic paths, ensuring identical results despite platform differences, while preserving freedom to adapt naming schemes without compromising integrity.
What Are Best Practices for Logging Integrity Events?
Best practices for logging integrity events emphasize deterministic, tamper-evident records, structured metadata, and immutable storage, enabling thorough authentication auditing and provenance benchmarking while maintaining clarity, traceability, and minimal performance impact for freedom-seeking teams.
How Scalable Are Checks for Large Research Datasets?
Scalability is contingent on architecture; checks for large datasets leverage dataset partitioning and scalable pipelines. Benchmarks reveal near-linear performance gains with partitioning, while maintaining reproducibility and auditability, enabling researchers to balance throughput, cost, and data integrity.
Conclusion
The batch demonstrates a disciplined approach to provenance, where identifiers, contexts, and transformations are tracked with cryptographic rigor. Decoding tags reveals lineage and custody steps, enabling verifiable trails. Integrity checks surface authenticity signals and anomalies, guiding trust decisions. For researchers and developers, the practical takeaway is to implement end-to-end verification and immutable logging as standard practice, leaving no stone unturned in data custody—a clockwork system that keeps everything clear and on track. In short, it’s a tight ship.





