Key points about sorry another account from your organization is already signed in on this computer
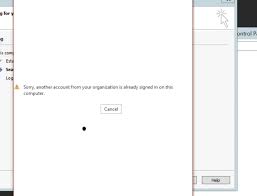
Have sorry another account from your organization is already signed in on this computer you ever been frantically trying to log into your organization’s account, only to be met with the dreaded message “sorry another account from your organization is already signed in on this computer”? It can be frustrating and confusing, but don’t worry – we’ve got you covered! In this blog post, we will break down the key points you need to know about this common issue and provide solutions to help get you back up and running in no time. So let’s dive in!
What to do if you see the
If you see the message “Sorry, another account from your organization is already signed in on this computer,” it means that someone else in your organization is already signed in to the computer with their own account.
If you need to use the computer, you’ll need to sign out of the other person’s account first. To do this, click on the profile icon in the top right corner of the screen and select “Sign out.” You can then sign in with your own account.
If you’re not sure who else has an account on the computer, you can check by going to the “Users” folder in the “File Explorer.” Double-click on the folder to open it and see a list of all users who have accounts on the computer.
How to prevent the
If you are using a work or school account, you may be signed in to multiple accounts at the same time. However, if you are using a personal Microsoft account, you can only be signed in to one account at a time. To prevent the “Sorry, another account from your organization is already signed in on this computer” error, make sure that you are only signed in to one Microsoft account at a time. If you are signed in to multiple accounts and need to switch between them, sign out of all accounts and then sign back in to the account that you want to use.
Conclusion
It is important for organizations to be aware of the potential problems caused when another account from their organization is already signed in on a computer. By understanding the key points related to this issue, they can then take appropriate steps to ensure that each user has access only to their own data and resources. Additionally, companies should ensure that each user’s permissions are properly set up so that no unauthorized access is granted. With these precautions in place, organizations can rest assured knowing that their users will always have the utmost security and privacy while using computers within the organization’s network.

![[pii_email_5c1227463021bd0531e8]](https://computertechlife.com/wp-content/uploads/2023/06/download-6.png)
![[pii_email_a37aeab4f52a36cfec65]](https://computertechlife.com/wp-content/uploads/2023/05/images-14.jpg)

