Review Call Record Authenticity Check – 3534301233, 3534586061, 3618665328, 3760966060, 3773924616, 3792914009, 3802425752, 3806919826, 3880911905, 3883440219
The discussion centers on a methodical review of call record authenticity for the listed numbers, focusing on provenance, metadata integrity, and tamper indicators. It emphasizes timestamp accuracy, caller ID consistency, and reproducible checks, all conducted under privacy and access controls. The approach favors auditable conclusions and cryptographic seals where applicable, ensuring traceability and independent review. A disciplined workflow remains essential, inviting practitioners to consider practical steps before moving to conclusions. The next section offers concrete verification steps and guardrails.
What Is Review Call Record Authenticity?
Review Call Record Authenticity refers to the verifiable accuracy and reliability of call recordings used for evaluation, compliance, or dispute resolution. The concept is methodical, evidence-based, and objective, detailing provenance, metadata, and tamper indicators. It remains focused on auditability rather than narrative nuance, avoiding unrelated topic digressions while acknowledging potential off topic distractions that do not compromise core verifiability and integrity measures.
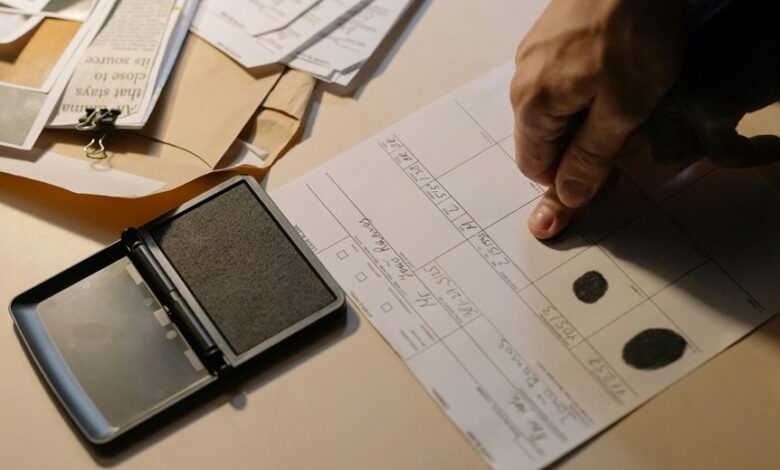
How to Verify Authenticity Across the Listed Numbers
To verify authenticity across the listed numbers, a structured, evidence-based approach should be employed that examines provenance, timestamp accuracy, caller IDs, and tamper indicators across each recording set.
The analysis emphasizes call record integrity and caller id verification, applying consistent criteria to provenance, metadata, cryptographic seals, and cross-reference checks, ensuring traceability while avoiding speculative conclusions.
Red Flags and Best-Practice Checks You Can Perform Quickly
Red flags and best-practice checks can be conducted rapidly by applying a predefined checklist that prioritizes verifiable indicators over speculative impressions.
The methodical process screens for anomalies such as inconsistent timestamps, unusual call durations, and mismatched metadata.
Results emphasize reproducible evidence, not intuition, ensuring a disciplined review that remains objective, avoiding unrelated topic digressions and off topic distractions.
A Practical, Privacy-Conscious Verification Workflow for Teams
The privacy preserving methodology defines access controls, audit trails, and minimal data exposure.
A rigorous verification workflow promotes traceability, independent review, and consistent conclusions without compromising confidentiality or operational freedom.
Conclusion
The audit treats each recording as a discrete artifact, yet the conclusion must interlink them. Juxtaposition highlights consistency versus variation: metadata coherence across timestamps and caller IDs contrasts with occasional tamper indicators or gaps. In rigorous, privacy-conscious terms, verifiable seals and reproducible checks anchor trust, while narrative interpretation remains constrained. The result is a methodical verdict: uniform provenance where seals align, and isolate anomalies where evidence suggests independent review or remedial action.